What is Point-to-Point Encryption (P2PE)?
Point-to-Point Encryption (P2PE) is an encryption standard established by the Payment Card Industry (PCI) Security Standards Council. It requires that payment card data be encrypted immediately upon use with the merchant’s point-of-sale terminal and cannot be decrypted until securely transported to and processed by the payment processor.
What is PCI-validated Point-to-Point Encryption (P2PE)?
A PCI-validated P2PE solution is a combination of secure devices, applications, and processes that encrypt credit card data immediately upon swipe or dip in the payment terminal (also called the Point of Interaction, or POI). The data remains encrypted until it reaches the Solution Provider’s secure decryption environment.
In order for a P2PE solution to receive validation from PCI, the solution, the Solution Provider, and associated players in the overall P2PE solution must undergo assessment and audit by a P2PE Qualified Security Assessor (QSA), before being brought before the Council for approval.
How Point-to-Point Encryption Works
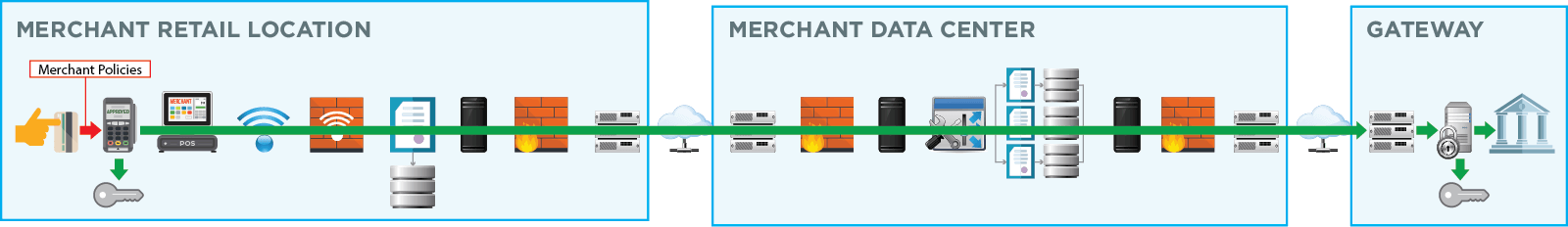
Point-to-point encryption is composed of the following steps:
Encryption at the point of transaction
Customer data is immediately encrypted at the source, whether that be a credit card swipe or tap. This ensures that private information is protected and rendered useless to bad actors while in transit.
Data transmission
This encrypted data is sent over to the payment processor. As a result, payment information cannot be used, even if intercepted.
Decryption Occurs at the Point of Payment
Data is decrypted only by the payment processor through a secure and private key. Payment processors use the information to finalize the payment.
The Differences between PCI-validated P2PE and End-to-End Encryption (E2EE)?
Below is an overview between E2EE and P2PE.
Non-Validated (Unlisted) Encryption Solutions
Encryption solutions that have not been validated by the PCI SSC, but still provide functions such as encrypting within the POI terminal and decrypting outside the merchant environment, are generally called unlisted P2PE solutions or End to End Encryption (E2EE) solutions.
PCI-Validated (PCI-Listed) P2PE Solutions
PCI-validated P2PE solutions have been assessed by a P2PE QSA as having met the PCI P2PE standard and are therefore listed on the PCI website under Approved P2PE Solutions. In addition to meeting the P2PE standard, the decryption component of the solution must operate within a secure environment that is annually assessed to the full PCI DSS standard.
| Point-to-Point Encryption | End-to-End Encryption | |
|---|---|---|
| Overview | This term is defined by the PCI Council and must meet specific standards. | This term is broader in nature and is not validated by the PCI Council |
| Compliance | These tools are assessed and audited by the PCI Council. Once approved, it is listed on the PCI website. | These tools are not assessed by the PCI Council. As a result, there can be more risk. |
| PCI Scope | P2PE will reduce PCI scope | E2EE may reduce PCI scope, but this will depend on how it is implemented. |
What is a PCI-validated P2PE Solution, and What Does it have to Include?
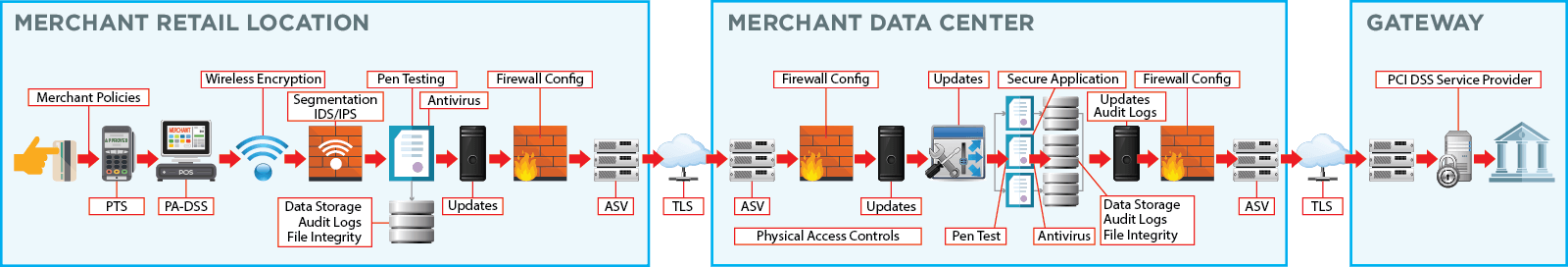
A PCI-validated P2PE Solution Provider is responsible for the design and implementation of a P2PE solution, and management of the solution for our partners and their merchants. We are also responsible for ensuring that all P2PE requirements are met, including any P2PE requirements performed by third-party organizations on our behalf (for example, hardware manufacturers, certification authorities, and key injection facilities).
A PCI-validated P2PE solution is required to have all of the following:
- Secure encryption of payment card data at the POI / i.e., the payment terminal
- P2PE-validated application(s) at the POI
- Secure management of encryption and decryption devices
- Management of the decryption environment and all decrypted account data
- Use of secure encryption methodologies and cryptographic key operations, including key generation, distribution, loading/injection, and administration
Benefits of PCI-validated P2E
Validated by the PCI Council
PCI SSC (Payment Card Industry Security Standards Council) was formed by major credit card companies in 2006 to set a standard for security best practices. Being approved by the PCI Council requires a rigorous testing process to be approved. If a solution has been validated by the PCI Council, companies can ensure they are better aligned with global payment security standards.
Reduced PCI Scope
Merchants who use a validated P2PE solution within their environment and keep this environment segmented from any card data from other channels (e.g., e-commerce) are eligible to complete the authorized self-assessment questionnaire SAQ P2PE that is known and accepted by all acquirers. Under PCI DSS v4.0, this represents a significant reduction of controls, reducing the number of questions by nearly 90% for merchants moving from the SAQ D (329 questions) to SAQ P2PE (21 questions). To put it simply, separating card data from the POS and other enterprise network systems allows merchants to reduce PCI scope and more efficiently manage controls or eliminate them completely.
Improved Security
Bad actors are getting more sophisticated in terms, as is evidenced by the number of data breaches online. In fact, there is an attack every 39 seconds and data breaches have grown every year since 2013. Malware is the preferred way for hackers to gain access to sensitive credit card data. They use this to scour the internet for unencrypted information, creating a big security risk for companies not implementing global best practices. As a result, it’s important that businesses stay vigilant.
A validated solution ensures heightened security since it reaches a specific threshold of requirements. Additionally, hackers cannot steal data if encrypted and rendered useless. This offers an added layer of protection for your organization.
How does PCI-validated P2PE work with EMV and Tokenization?
PCI-validated P2PE protects data in transit. The role of P2PE is to immediately and fully encrypt all cardholder data within the payment terminal so it does not enter the POS as clear-text card data. By using strong encryption, device management practices, and key management, P2PE is effective at addressing the risk of card data compromise for card data in transit out of the merchant network as it is transmitted to the gateway or acquirer for decryption and processing.
Tokenization enables merchants and enterprises to safely “store” cardholder data at rest for use in future transactions. Tokenization is the technology where secure card data storage is centralized and a different value is used to represent the original cardholder data. When ready to be re-used, the token must generally be passed to the tokenization provider, where the original cardholder data is retrieved, decrypted, and utilized.
EMV authenticates the credit or debit card at the point of sale by reading a chip embedded on the card and validating the cardholder with their signature. EMV makes it extremely difficult (though not impossible) to “white-label” or duplicate a physical credit card that could then be used by thieves to purchase items at the POS.
Case Study: Hillman Partners with BlueFin to Secure Payment Information
While many solution providers advertise their security features, it was important to Hillman to partner with a provider that was accredited by the PCI Council. The Hillman Group also operates a large network of sel-service kiosks, and they wanted to reduce the PCI DSS requirements related to credit card payments.
Hillman chose to partner with BlueFin, since their solution extended beyond SRED hardware encryption offered by many providers. Instead, BlueFin was able to offer PCI-validated point-to-point encryption. Todd Spangler, SRVP & General Manager, The Hillman Group, noted, “We’re excited to offer a world-class payment processing system that ultimately provides our customers with sound peace of mind. It’s been a pleasure working with Bluefin to develop a strategy, technical solution, and action plan to achieve our final product.”
Bluefin’s P2PE Solution: The Gold Standard in POS Encryption & P2PE Encryption
In 2014, Bluefin became the first provider of a PCI-validated point-to-point encryption (P2PE) solution in North America. Today, our P2PE solutions are offered by Bluefin and through our 300 global partners in 60 countries.
With Bluefin’s PCI-validated P2PE solution, we encrypt cardholder data at the POI in a PCI-approved PTS device running P2PE validated software, and decryption is done off-site in an approved Bluefin Hardware Security Module (HSM). Our solution prevents clear-text cardholder data from being present in a merchant or enterprise’s system or network, where it could be accessible in the event of a data breach.
Note: “Only Council-listed P2PE solutions are recognized as having met the rigorous controls defined in the PCI P2PE Standard for the protection of payment card data, as well as meeting the requirements necessary for merchants to reduce the scope of their cardholder data environment (CDE) through use of a P2PE solution.”
Which Bluefin Products Offer PCI P2PE?
Every product provided by Bluefin includes PCI-validated P2PE. Our P2PE solutions include:
- PayConex Payment Gateway – Card present and card-not-present (CNP) payment processing for U.S. and Canadian companies
- PayConex for Salesforce – Card present and CNP payment processing for U.S. and Canadian companies utilizing Salesforce; a 100% integrated application
- QuickSwipe Mobile – iOS, Android and web-based payment processing for U.S. and Canadian companies
- Decryptx – Stand-alone, P2PE solution decoupled from payment processing; available to global processors, payment gateways and software vendors
Frequently Asked Questions
About Point-to-Point Encryption
Is Point-to-Point Secure?
Point-to-point encryption is very secure and must meet rigorous requirements set forth by the PCI Council to be considered a point-to-point solution.
What is a Point-to-Point Encryption System?
A point-to-point encryption system is the solution used for P2PE. This system has been independently audited and assessed by the PCI Council to ensure it meets global security standards.
What are the common encryption techniques?
Symmetric and asymmetric encryption are the most common types of encryption. For symmetric encryption, the same key is used throughout the entire process, while asymmetric encryption uses a separate key for encryption and decryption.
About BlueFin
Which Integrated Partners Provide Bluefin’s P2PE Solution?
Bluefin is the only P2PE solution provider that has “decoupled” P2PE from payment processing with our Decryptx product, enabling processors, payment gateways and software vendors to provide our P2PE solution through their platforms.
Any merchant or organization utilizing one of Bluefin’s partners can get the security and reduced PCI scope of our P2PE solution through their current configuration. Example partners are listed below, or you can access our full list.
- Healthcare: Epic, Flywire, Paya, HealthPay 24, Phreesia
- Higher Education: Paciolan, Nelnet Campus Commerce, TouchNet, Blackbaud, Blackboard, AudienceView, Modern Campus
- Retail: Verifone, NCR, CyberSource, Volante, Transaction Network Services.
- Other: Aspira, DataCap Systems, Powertranz, Kubra, Payscout, Payway, Unberboeck Systems
Additionally, any platform provider globally can partner with Bluefin for Decryptx via a simple API. Learn more about our Decryptx partner program or contact us.
How Does Bluefin Implement PCI P2PE for Organizations?
Bluefin is your partner in payment security and will be there every step of the way in P2PE implementation and activation.
Our implementation options vary by product, organization size and configuration.
- For small to medium-sized businesses utilizing Bluefin’s products, our clients work directly with our inside sales team on device ordering and setup. They are available to answer any questions that you may have and walk you through the process of using your P2PE device. They will also get you started with our P2PE Manager® portal for device check-in, activation, monitoring and P2PE attestation. Additional questions after initial setup by the sales team can be addressed by contacting our Customer Service team.
- For large enterprises, our clients work directly with a dedicated Relationship Manager. Your Relationship Manager will guide you through the implementation options, depending on your environment and partnerships, while also engaging our integration team for any necessary development. Consultation and management is free of charge.
For partner clients, Bluefin will assist in the above steps but depending on the partnership, organizations may need to contact their partner provider for integration and support. If you are unsure of whether Bluefin or your provider offer integration and support assistance, contact us.
What is the P2PE Manager®?
As part of Bluefin’s P2PE program, all clients and partners have access to Bluefin’s P2PE Manager – the only 100% online portal for P2PE device chain of custody and attestation – free of charge.
The P2PE Manager simplifies management, reporting and attestation for your organization. The Manager records the complete lifecycle of each device that you deploy, from the time the device is ordered, to shipment, to receipt, to activation. You can also set up locations for the devices, assign an administrative hierarchy for user access, view transactions, and export reports for attestation.
The P2PE Manager is also offered as a tool for other P2PE solution providers or organizations seeking to simplify device management for their users. Contact us to learn more.
Can Decryptx Partners List their Bluefin P2PE Solution on the PCI Website?
Yes, one of the benefits of our Decryptx partner program is that all of our partners are eligible to include their P2PE solution as a “sub-listed” solution under Bluefin’s P2PE listing. A sub-listing enables your organization to be listed under our P2PE certification with your own product name for the PCI-validated P2PE offering. Learn more about our sub-listing option or contact us directly.
Bluefin can work directly with your organization to create a custom P2PE solution. Our relationship managers will work with you one-on-one to understand your processing environment, your acceptance channels and your partnerships to craft a solution for your unique business case.
Can Bluefin Create a Custom P2PE Solution for my Organization?
Additionally, for large retailers and other organizations, we can provide our Direct to Merchant P2PE solution, which can be accessed through a direct connection to Bluefin – making our P2PE option available with no change to a retailer or enterprise’s processing environment. This is an ideal solution for large companies interested in a direct P2PE program. Benefits include:
- Simple Implementation: Bluefin provides several configurations and options for P2PE direct, including coding directly to our Decryptx API from your data center to eliminate customer and employee endpoints, networks, and environments from PCI scope.
- Customization: Our direct P2PE solution allows your organization to easily modify your existing payment ecosystem with the largest selection of P2PE payment terminals and Key Injection Facilities (KIFs) available in the market, including Remote Key Injection (RKI).
- Premier Support: Bluefin can support and manage the requirements for all components included in a validated P2PE solution (Domains 1-6), including encryption management services, the decryption environment, chain-of-custody, RKI and KIFs.
Contact us to learn more.
What P2PE Devices / Key Injection Facilities (KIFs) Does Bluefin Offer?
Bluefin has the distinction of being the leading PCI-validated P2PE solution provider with the largest number of device and KIF offerings. Our full list of devices can be accessed on our P2PE Device page, but we provide countertop, mobile, call center and unattended devices from a variety of manufacturers, including:
- Anywhere Commerce
- AMP
- BBPOS
- Datecs
- Equinox
- ID Tech
- Ingenico
- Magtek
- Miura
- PAX
- Verifone
*Note that all devices may not be available across all partners and all Bluefin products. Contact us to learn more about devices and configurations.
Bluefin is currently partnered with 16 KIFs globally to provide our solutions. These include:
- CDE – Atlanta, GA
- Datecs – Sofia, Bulgaria
- First Data Hardware – Atlanta, GA and Mississauga, ON
- Fiserv – Brookfield, WI
- Infinite Peripherals – Irvine, CA
- Ingenico Group – Atlanta, GA and London, UK
- Lantec – Dublin, UK and Poland
- Maxwell Merchant Solutions – Belleville, ON
- PayCipher – Alpharetta, GA
- POS Portal – Sacramento, CA and Louisville, KY
- SecureRetail – Leicestershire, UK
- Spencer Technologies – Northborough, MA
- UCP – Las Vegas, NV
- Verifone – San Jose, CA