Tokenization as a Service
ShieldConex®
ShieldConex® delivers Tokenization as a Service (TaaS) to protect payments, Personally Identifiable Information (PII), and Protected Health Information (PHI) across every channel. By replacing sensitive data with secure, vaultless tokens, ShieldConex reduces PCI DSS scope, helps meet global data privacy mandates, and minimizes breach risk. With flexible deployment – API, iframe, or secure batch workflows via FileGuard – ShieldConex provides universal, scalable protection without disrupting existing systems.
Ensure Compliance
Tokenize PAN, PII, and PHI to reduce PCI scope and stay ahead of data privacy regulations with minimal effort.
Secure Structured Files
Protect ACH, CSV, and fixed-width files over secure SFTP, securing sensitive data in legacy systems and batch workflows.
Minimize PCI Scope
Lower compliance costs and complexity by reducing PCI DSS scope across payments and third-party integrations.
Reduce Risk
Replace sensitive information with vaultless tokens to minimize exposure and reduce breach liability.
Cloud-Based
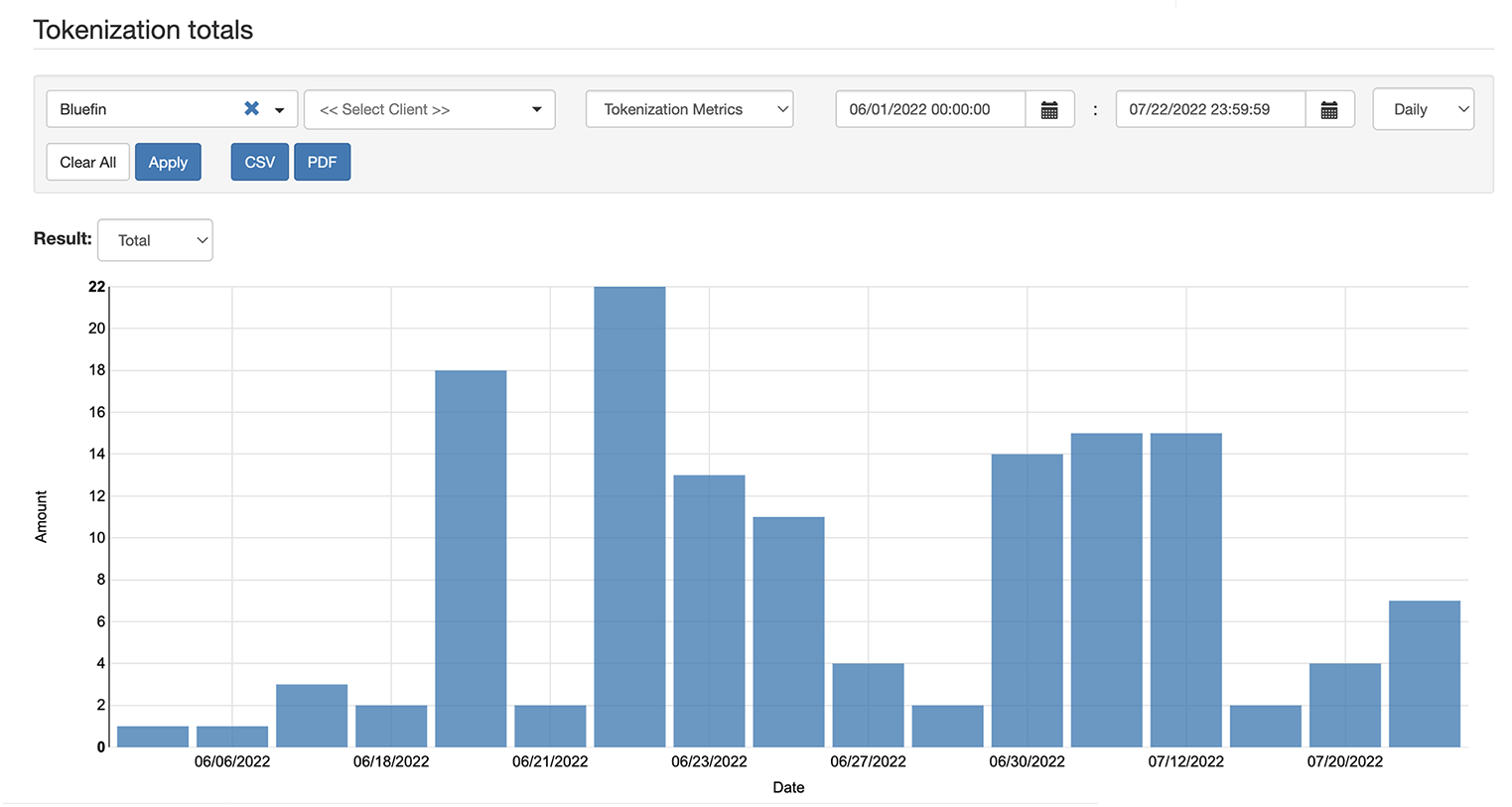
Manage tokenization through a cloud-native portal with real-time analytics, easy user controls, and seamless scalability.
Vaultless Tokenization for Any System, Anywhere
Security-First Architecture
Flexible, Scalable, Protected
-
Cloud-Native and API-Driven
Deploy tokenization without hardware or infrastructure changes.
-
Vaultless, Format-Preserving Tokens
Protect payments, personal, and health data while preserving data usability.
-
FileGuard Batch Protection
Tokenize and detokenize structured files (ACH, CSV, fixed-width) via secure SFTP for legacy workflows.
-
Instant Data Protection
Tokenize data at intake before it enters your environment, ensuring PCI DSS, HIPAA, and GDPR compliance.
-
Payment Flexibility
Enable card-on-file storage, recurring billing, refunds, and omnichannel continuity.
-
Effortless Management
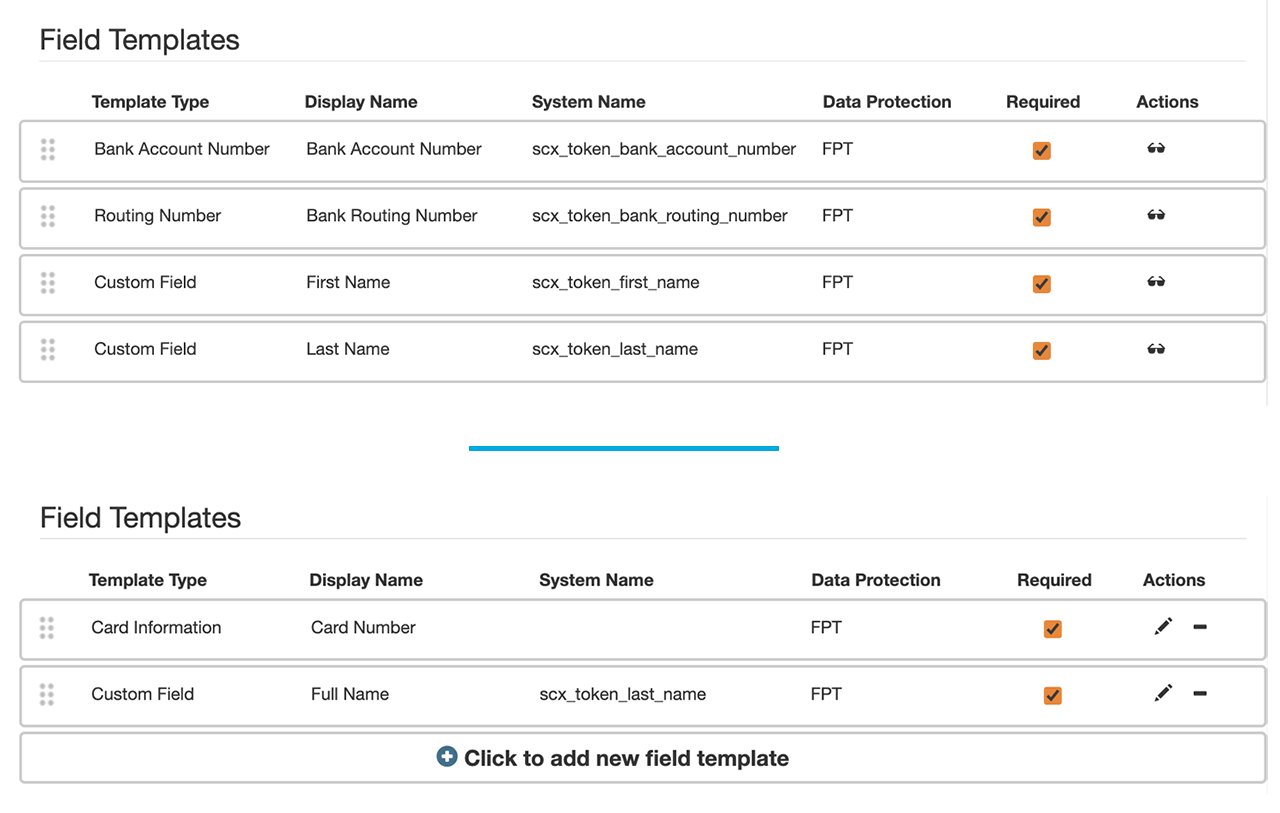
Use ShieldConex Manager to configure templates, manage users, and track tokenization metrics – all in one dashboard.
Secure File-Based Workflows with FileGuard
Extend ShieldConex tokenization to NACHA, CSV, and other file formats. FileGuard secures sensitive data in motion and at rest, enabling compliant, SFTP-based workflows without disrupting existing systems.
Tokenization is a broad and complicated topic with many types of tokens and different token service providers. Over time, it’s common for business relationships and partnerships to change, and moving to a new tokenization service can cause disruptions. A solution that insulates merchants from tokenization changes, and gives them the freedom to switch or add new payment partners at will, greatly simplifies the effort of doing business in today’s fast-paced environment.
David Mattei, Strategic Advisor, Fraud & AML practice – Datos Insights
The Power of Tokenization in Modern Security
FAQ About ShieldConex and Data Tokenization
What is the ShieldConex Tokenization Platform?
ShieldConex is Bluefin’s vaultless tokenization platform that secures any PII, PHI or payment element entered online. Our cloud-based solution can be implemented via API or an iFrame. Users can choose to protect their data with either Format Preserving Tokenization (FPT) or Format Preserving Encryption (FPE). ShieldConex also provides omnichannel tokenization across the POS and online, and in 2023, will support network tokenization.
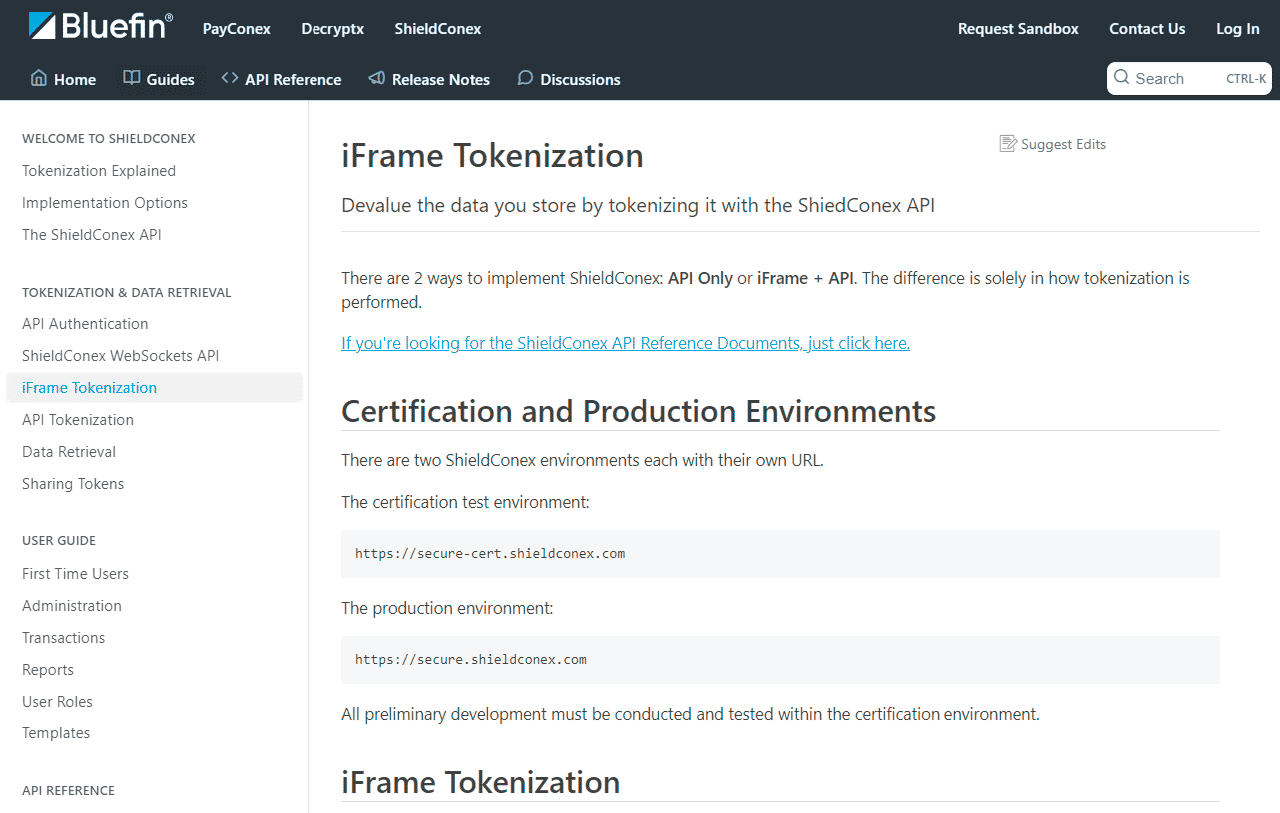
How are iFrames Used within ShieldConex?
The use of an iFrame allows ShieldConex customers to outsource the capturing of sensitive data, in a scenario where the end-user sends its data directly to Bluefin for tokenization without traversing the customer’s production systems. This allows for greater scope (and therefore risk) reduction of the Page customer environment as no sensitive data is ever handled by those front-end systems in terms of transmission, processing or storage. The responsibility for the capture and encryption of this data rests with Bluefin as a Tokenization Service Provider.
The use of iFrame Forms in the capture of data means that once the end-user enters the data to a data capture form, the sensitive data is sent directly to Bluefin’s servers for tokenization and only the tokenized data need be received by the partner. This removes the transmission, processing and storage of the sensitive data elements from the partner environment and Bluefin effectively acts as a tokenization service provider without the need to store its own copy of the tokenized data. Neither the partner organization nor Bluefin possesses the original clear text data.
How Does ShieldConex Perform Omnichannel Tokenization?
ShieldConex has the ability to always create the same token for the same input value. For example, the same credit card number can always generate the same token. So, if the credit card number comes from a mobile phone, a website, or even a payment terminal, ShieldConex can always generate the same token from the same credit card number. This gives the business the ability to affiliate the tokenized card number with the customer – so whenever that token is used, the business can immediately identify the customer while never having access to the real credit card number. This feature, when combined with the partner token sharing feature in ShieldConex, can solve some complex business requirements for the business and their affiliates.
What is FileGuard and how does it relate to ShieldConex?
FileGuard is Bluefin’s file-based extension of the ShieldConex platform, designed to tokenize and detokenize structured files such as NACHA, CSV, and fixed-width formats. It enables organizations to securely process sensitive data in batch workflows – like payroll, vendor payments, or tuition disbursements – using secure SFTP transfers. FileGuard brings modern data protection to legacy systems without requiring any major infrastructure changes.
Is There Any Latency in Tokenization or Detokenization?
In legacy “vaulted” tokenization solutions, data is stored on a token server and must be retrieved to use. This form of tokenization requires large databases to map tokens to their original data.
Unlike those legacy vaulted solutions, ShieldConex leverages vaultless tokenization. In this case, tokens are generated using Hardware Security Modules (HSMs), eliminating the need for storing any sensitive data. Typical response times are about 1/10th of a second – not perceptible by humans – meaning data is available instantaneously.
Does ShieldConex Store Data?
ShieldConex is a “vaultless” token solution, so the actual data is never stored in a “vault” or database. Secured data can be unmasked at any time by calling the ShieldConex service using your assigned API key.
Can ShieldConex Secure Data Through a Mobile Application?
Yes, ShieldConex also protects data in a mobile environment. If the app is written in a native app framework, the app would need to call Bluefin’s ShieldConex API. If the app is written within a web app framework, it will be able to either leverage the ShieldConex API or leverage the ShieldConex iFrame, depending on your organization’s preference.
Can ShieldConex Protect my Webpage from Being Compromised?
ShieldConex can add protection. When using the ShieldConex iFrame, the sensitive data is being captured by ShieldConex directly – not on the webpage of the customer. It also requires an out-of-band, 2-step process to retrieve this data from ShieldConex, adding an additional layer of security. Even with this in place, Bluefin recommends:
- Regularly analyze all of your own website scripts throughout the development lifecycle
- Implement client-side protections such as web skimming or malware protection
- Deploy a bot management solution that is able to detect and defend against sophisticated botnets that result from browser-based attacks.
How is ShieldConex Implemented?
ShieldConex is an entirely cloud-based product that leverages APIs and secure iFrames configured through our ShieldConex Manager administration portal. Bluefin will provide access to the ShieldConex APIs, login credentials to ShieldConex Manager, and online integration documentation. We also provide integration assistance as needed to get your organization live with ShieldConex in a timely and successful manner.
How do I Determine if the iFrame or API Option is Right for my Organization?
The iFrame is specifically intended to capture data entered by a person into a web form. Typically, when PCI data is captured on a website, this brings the site into PCI scope, requiring additional work to make it PCI DSS compliant. With the iFrame, Bluefin hosts the data capture and is responsible for maintaining a PCI DSS compliant site, thereby reducing the time and effort required to implement PCI data capture.
If you’re capturing data in a web form, but have strict controls and requirements for the user interface, then API tokenization allows you to maintain full control over the user interface. However, the additional overhead of maintaining compliance should be considered.
If you need to tokenize data that is not being manually entered, then API tokenization is the right solution for you.
Secure sensitive data with vaultless tokenization
Let’s connect.
"*" indicates required fields