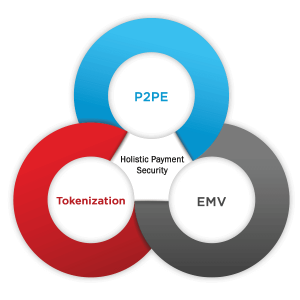
The payment industry around the world has adopted EMV for production and transaction support for credit cards issued with integrated chips in order to provide new card fraud protections for consumers. But how does EMV technology protect against fraud, and what other security technologies can be used in tandem to bolster data security strategies?
The Role of EMV – Securing Against Counterfeit Cards
Over the last few years, the United States has made a gradual shift toward EMV technology. To help this transition, major card brands have instituted phased liability shifts, where card present merchants or credit card issuers who fail to support these cards may be liable for counterfeit card fraud. Important liability shift dates include:
- October 2015, which affected most credit card networks and industries
- October 2016 for ATMs accepting MasterCard
- October 2017 for other ATM cards
- April 17, 2021 for automated fuel dispensers
The EMV chip embedded within the new chip cards is capable of using advanced cryptography to generate a unique code, or iCVV, which is then sent to the card networks with each transaction to confirm that the physical card is legitimate. This process has been demonstrated to be effective at preventing fraudsters from creating counterfeit cards.
However, the EMV chip does not provide any encryption for the credit card primary account number (PAN), expiration date or cardholder name, three sensitive data elements classified as cardholder data and required to be protected according to PCI DSS.
In summary, EMV is primarily effective for reducing card-present fraud by securing against counterfeit cards.
The Role of P2PE – Securing Card Data in Flight
Forensic investigations have confirmed that the preferred method for extracting account data from point-of-sale (POS) systems has been the use of RAM-scraping malware. This breed of malicious software is able to access clear-text card data as it is processed within system memory, even if the system uses encryption to receive and retransmit this sensitive data. While card data may be received by the POS system in encrypted form, encrypted when stored, and encrypted when transmitted, it is unencrypted while in memory and therefore is highly vulnerable to this type of attack.
The role of P2PE is to immediately and fully encrypt all cardholder data within the payment terminal. By using strong encryption, device management practices, and key management, P2PE is effective at addressing the risk of card data compromise for card data in transit out of the merchant network as it is transmitted to the gateway or acquirer for decryption and processing.
There are two types of terminal encryption: PCI-listed P2PE solutions and unlisted solutions (sometimes called end-to-end encryption or E2EE). While there are many nuanced differences between PCI-validated and non-validated P2PE, there are three high-level requirements that every P2PE/E2EE solution must offer:
- The card data must be encrypted using strong cryptography
- The encryption must be performed within a secure hardware device
- It must not be feasible to decrypt the data within the merchant environment
Through this process, P2PE performs the function of devaluing the cardholder data in the eyes of any hacker who may otherwise seek to access this information within the merchant’s software, systems, and network, therefore securing card data in-flight.
The Role of Tokenization – Securing Card Data at Rest
Finally, there are merchants who must perform certain customer billing functions such as delayed charges, subscriptions, refunds, or credits, which require credit card information.
Tokenization is the technology where secure card data storage is centralized and a different value is used to represent the original cardholder data. When ready to be reused, the token must generally be passed to the tokenization provider, where the original cardholder data is retrieved, decrypted, and utilized.
To take full advantage of the benefits of tokenization, PCI SSC recommends that merchants tokenize sensitive data as quickly as possible, replace cardholder data with tokens wherever it is stored, and use services that do not provide a mechanism to “detokenize” data, as this presents another avenue that may be exploited. When properly implemented, use of tokenization instead of storing actual cardholder data is valuable for securing card data at rest.
The Impact of PCI-Validated P2PE
Learn more about why validated encryption solutions and their importance in our white paper, “The Impact of PCI-Validated P2PE,” authored by our P2PE QSA Coalfire.® The three major sections of this whitepaper discuss:
- What is the role of P2PE, EMV and Tokenization in securing payments?
- What are the differences between PCI-validated and non-validated P2PE solutions?
- What is the Return on Investment (ROI) and Total Cost of Ownership (TCO) of a PCI-validated P2PE solution?